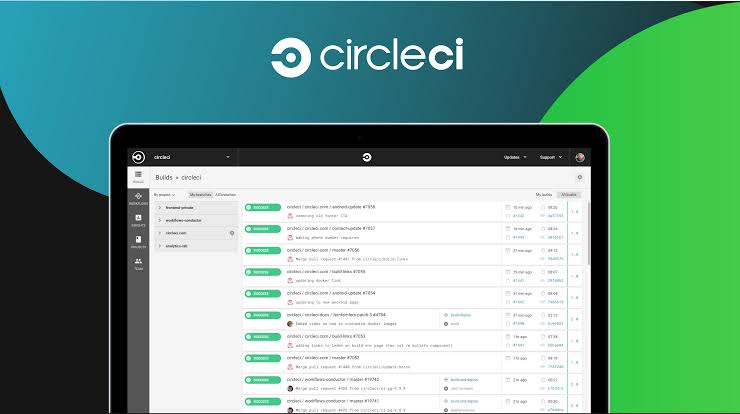
DevOps platform CircleCI disclosed that unidentified threat actors compromised an employee’s laptop and leveraged malware to steal their two-factor authentication-backed credentials to breach the company’s systems and data last month.
The sophisticated attack took place in mid December 2022 and that the malware went undetected by its antivirus software led to malware attack on laptop of engineer of CircleCI.
The malware was able to execute session cookie theft which enable them to impersonate the targeted employee in a remote location and then escalate access to a subset of our production systems.
Analysis of the security lapse revealed that the unauthorized third-party pilfered data from a subset of its databases and abused the elevated permissions granted to the targeted employee. This includes customer environment variables, tokens, and keys.
The threat actor believed to have engaged in reconnaissance activity on 19 December2022, following it up by carrying out the data exfiltration step on 22 December 2022.
The development comes a little over after week CircleCI urged its customers to rotate all their secrets.
All the data exfiltrated was encrypted at rest and the third-party extracted encryption keys from a running process which enable them to potentially access the encrypted data.
Upon learning that the customer’s OAuth token compromised and it proactively took the step of rotating all GitHub OAuth tokens.It worked with Atlassian to rotate all Bitbucket tokens . It revoked Project API Tokens and Personal API Tokens and notified customers of potentially affected AWS tokens.
It also limit access to production environment.It has incorporated more authentication guardrails to prevent illegitimate access even if the credentials are stolen.
Moreover it plans to initiate periodic automatic OAuth token rotation for all customers to deter such attacks in the future beside introducing options for users to “adopt the latest and most advanced security features available.